- QATestLab Blog >
- QA Basics >
- Types of Software Testing >
- IoT Testing >
- How One Robot Vacuum Incident Exposed a Serious IoT Risk
How One Robot Vacuum Incident Exposed a Serious IoT Risk

Connected devices are built to make everyday life easier. They clean our homes, monitor spaces, manage temperature, and respond to commands in real time. That convenience is exactly what makes incidents like this so important. When a weakness appears in the logic of a connected product, its impact can extend far beyond the device itself. The recent robot vacuum case is a clear example of how that can happen.
What Actually Happened
In February 2026, a software engineer in Spain started with a simple idea: to control his robot vacuum with a custom app(1). What he discovered went far beyond that.
Once connected to the backend system, he gained access to his own vacuum and to thousands of others across different countries. The product did not properly restrict what each device could access.
As a result, he was able to:
- control how devices move
- turn them on and off remotely
- access floor maps of private homes
- retrieve data collected inside those environments
For devices with cameras or microphones, this level of access could also extend to live audio or video.
What makes this case especially important is how that access was obtained. There was no traditional break-in. The engineer used a valid connection, but the backend system failed to enforce proper separation between devices. That is what made the incident so revealing: the product could appear fully functional, while the system behind it still allowed the wrong access in the wrong context.
The engineer publicly disclosed these vulnerabilities to draw attention to the risks posed by connected devices and to encourage manufacturers to improve how access and data protection are handled.
Why Different IoT Products Can Share the Same Weakness
This case is only one example. Similar issues are not limited to a single product type.
The same kind of weakness can affect:
- robot vacuums and home cleaning devices with cameras
- smart locks and access control systems
- baby monitors and home security cameras
- connected thermostats and energy management systems
- industrial IoT sensors and remote monitoring equipment
These products do very different jobs, but many rely on the same connected logic: cloud access, data exchange, command handling, and backend-controlled permissions. When those controls are weak or incomplete, similar issues can appear across very different products.
This risk is also becoming more visible. Modern tools make it easier to analyze connected systems and identify weak points, even in products that seem stable in everyday use. For users, this means that everyday connected devices may expose more data or functionality than expected if these gaps are not properly addressed.
The Business Impact Behind Technical Gaps
In connected products, a flaw rarely stays limited to code or infrastructure. Once it affects what a device can access, how it behaves, or what data it can expose, the issue quickly becomes public and business-critical.
The media start covering the story. Trust in the product weakens. Questions appear around how the issue was missed, how quickly the team responded, and whether the fix can really be trusted. That is exactly what happened in this case, where the incident drew broad attention, raised regulatory concerns, and left doubts about the fix’s completeness.
For IoT manufacturers, technical gaps can quickly turn into business problems. They affect reputation, increase post-release costs, and create pressure that is much harder to manage after public disclosure.
Why IoT Products Need More Than Feature Testing
This case highlights a gap that often remains invisible until something goes wrong.
A connected product can perform well in everyday scenarios and still behave incorrectly at the system level. Features, integrations, and user flows may appear stable, but they do not guarantee the correct handling of data, access, and interactions across the system.
At QATestLab, we approach IoT testing from this system-level perspective, treating a connected product as a full system — including the device, firmware, mobile app, cloud services, and backend logic.
To validate this, testing should cover:
- End-to-end validation across the full system
Device, app, and backend tested together to validate real data and command flows - Access boundaries between devices and users
Ensuring each device can access only its own data and functions - Behavior under non-standard interactions
Testing unexpected inputs, custom clients, and unusual request patterns - Connectivity and real network conditions
Testing behavior under interruptions, delays, weak signals, and reconnections - Firmware and update consistency
Checking whether firmware changes or OTA updates affect system behavior and interactions - Stability over time and under repeated use
Verifying behavior under load, repeated actions, and long-running scenarios
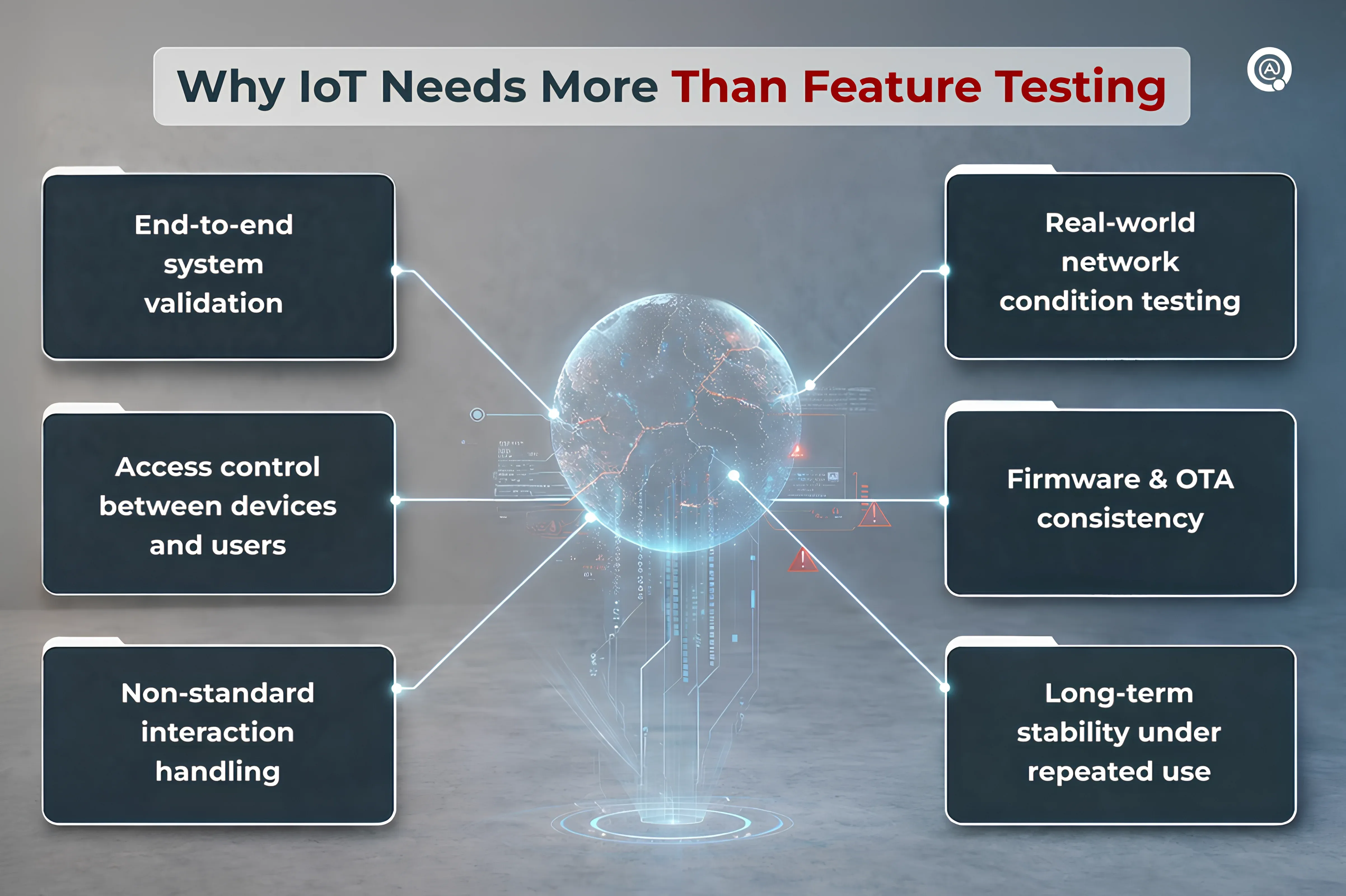
In IoT, many of the most important risks appear only when the full product is tested as a connected system under realistic conditions.
Final Thought
The case shows how a weakness in connected system logic can become a real user-facing risk once a product reaches the market. In IoT, issues rarely remain isolated, because devices depend on cloud services, backend rules, data flows, and interactions that must work together reliably. Incidents like this also highlight why both manufacturers and users need to better understand how connected devices handle access, data, and control.
That is why connected products should be validated as full systems under realistic usage conditions. At QATestLab, we help teams test IoT products across devices, firmware, cloud, and integrations to identify risks earlier and support more confident releases. If you would like to validate your connected product, feel free to contact us.

Sources
Learn more from QATestLab
Related Posts:
About Article Author
view more articles



